Go to address “chrome://version/” in Chrome address bar. Profile Path will be displayed in addition to other Chrome details.
Security Now – uBlock Origin to the rescue
Everyone is annoyed by the pervasive cookie permission
banners which compliance with the European Union’s GDPR
has forced upon the world. I recently realized that I had
become similarly annoyed by another increasingly
pervasive website feature, which is the proactive offer to
sign into whatever website I may be briefly visiting…
Chrome 122 New V8 security setting
Chrome address bar: chrome://settings/content/v8
Default is to Sites can use the V8 optimizer
Set to Don’t allow sites to use the V8 optimizer
Can add Customized behaviors for specific sites if trouble occurs with a specific site
From Chrome Enterprise and Education release notes
Last updated on: February 16, 2024
New V8 security setting back to top
Chrome 122 adds a new setting on chrome://settings/security to disable the V8 JIT optimizers, to reduce the attack surface of Chrome browser. This behavior continues to be controlled by the DefaultJavaScriptJitSetting enterprise policy, and the associated JavaScriptJitAllowedForSites and JavaScriptJitBlockedForSites policies. The setting is integrated into Site Settings. The enterprise policies have been available since Chrome 93.
Chrome 122 on ChromeOS, LaCrOS, Linux, MacOS, Windows, Fuchsia
Nice cookie banner
Discovered nice cookie banner at the Security Now website.
Also, nice details on cookies at What are cookies?
Thanks Microsoft Teams, but it is October!?!?
Received this popup today on my Windows Desktop from the Teams malware:
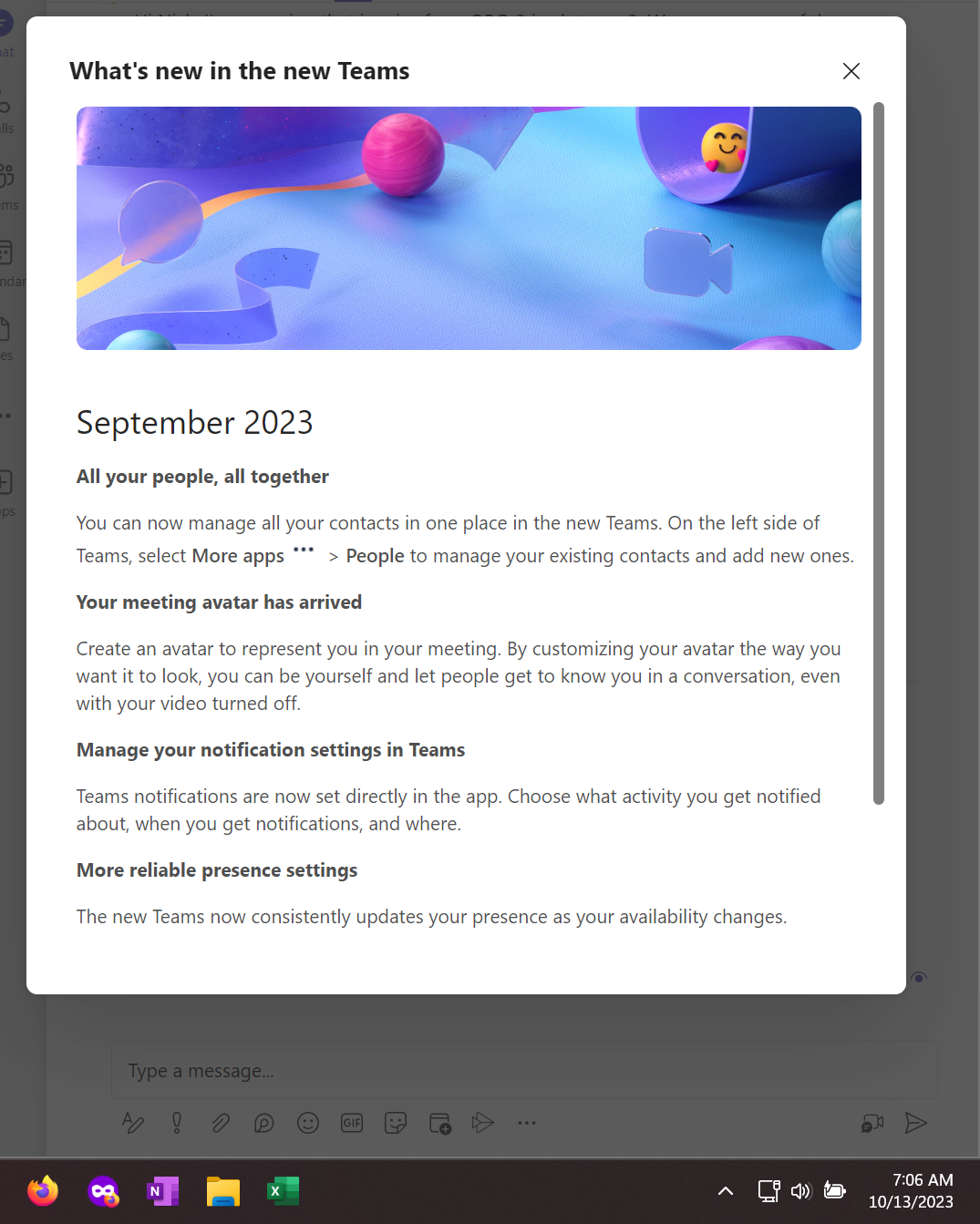
Thanks, but it is October 13th. WTF?!?!
Azure Arc Setup – Thanks Microsoft
Azure Arc Setup is now on my servers and I don’t remember asking or installing it!!!
Good take here by C:Amie (not) Com!
Start menu item:
System tray/notification area item:

Hard reset of Chrome user settings
Chrome reset
Close all chrome.exe instnaces
Go to folder %USERPROFILE%\AppData\Local\Google\Chrome
Rename folder User Data to User Data.old
Launch Chrome
Chrome cache folder: %USERPROFILE%\AppData\Local\Google\Chrome\User Data\Default\Cache
Computer\HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\User Shell Folders
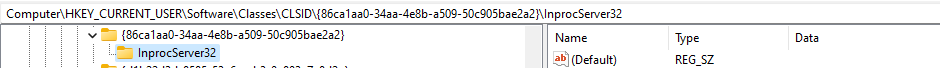
Bring back old school context menu for Windows 11
command prompt or modern terminal
reg.exe add “HKCU\Software\Classes\CLSID\{86ca1aa0-34aa-4e8b-a509-50c905bae2a2}\InprocServer32” /f /ve
or
Computer\HKEY_CURRENT_USER\Software\Classes\CLSID\{86ca1aa0-34aa-4e8b-a509-50c905bae2a2}\InprocServer32
Enable content Copy/Paste between VMRC client and Windows/Linux VM
Useful tip from VMware
Enable content Copy/Paste between VMRC client and Windows/Linux Virtual Machine (57122)
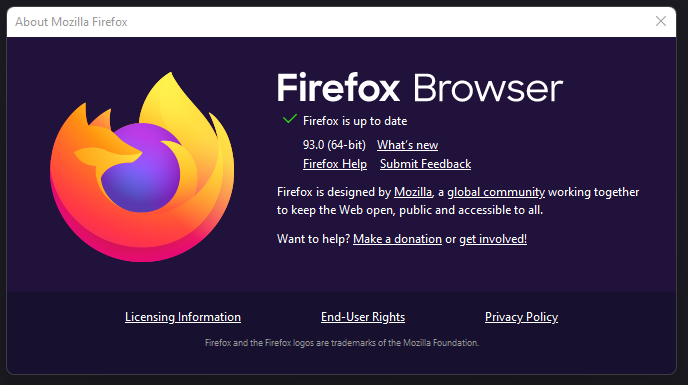
Firefox – Updates disabled by your system administrator
Trouble:

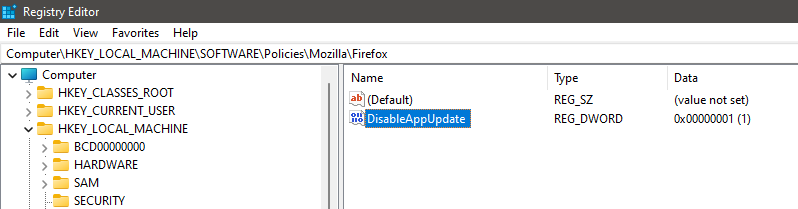
Fix:
- Regedit
- Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Mozilla\Firefox
- Set DisableAppUpdate value to 0
- Close Firefox
- Open Firefox
- Settings > Help > About
- Firefox will attempt to update or display that it is up to date